need help here,ty
Looks like it is working.
You can search for your relay by name, contact ID or fingerprint here: Relay Search
moved to LINUX
but for now nothing appear(relay search),now i setup using linux, cause on windows got a problem,sudo ARM also nothing hppen, cat /var/lib/tor/fingerprint no file
Your server’s fingerprint will show up in the console when starting tor.
Example from one of my nodes:
[...]
Dec 12 11:34:13.000 [notice] Configured to measure statistics. Look for the *-stats files that will first be written to the data directory in 24 hours from now.
Dec 12 11:34:13.000 [notice] Your Tor server's identity key fingerprint is 'gbt2USicebeer01 D51AE2FB1D699B2D9FB11F2B048E7E035C984B4B'
[...]
=> Fingerprint for this node is “D51AE2FB1D699B2D9FB11F2B048E7E035C984B4B”. Look it up in the relay search and you’ll find it: Relay Search
You can also search for “gbt2USicebeer01” and you will find the same. It’s the name I gave the node in my torrc-file:
[...]
Nickname gbt2USicebeer01
[...]
Try the same for your relay and be aware that the search can take a couple of hours for new nodes to show up.
here my setup:
ORPort 443**
Exitpolicy reject :
Nickname xxxxx
ContactInfo xxxxx
ccountingStart day 0:00
AccountingMax 512 MBytes
RelayBandwidthRate 5120 KBytes
RelayBandwidthBurst 10240 KBytes
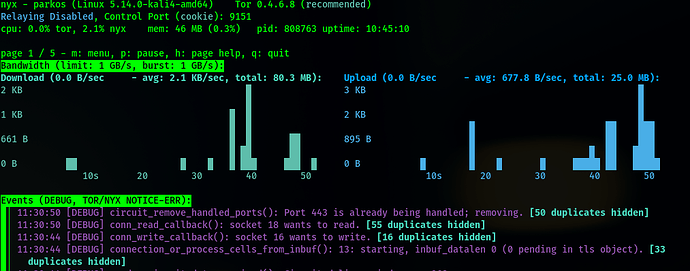
ARM is deprecated & replaced by Nyx. Nyx is a command-line status monitor written in Python for Tor. Nyx funcitons much like top does for system usage, providing real time statistics,
http://3ewfgrt4gzfccp6bnquhqb266r3zepiqpnsk3falwygkegtluwuyevid.onion/index.html
i just wait for 6 hour. fingerprint still not availble,your info now very clear,thanks for concern man
very clear thnks so much mate
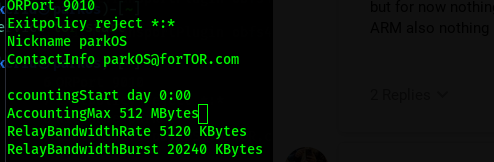
here my setup
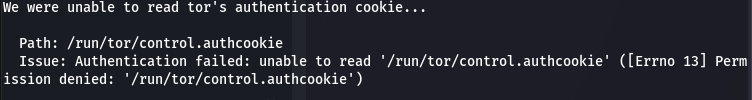
You’ll need to edit the torrc. Kali is based on Debian, so these instructions should work for you:
sudo nano /etc/tor/torrc
Remove the # character from lines ControlPort 9051 and CookieAuthentication 1 (line ~57)
Save Nano Command:
Ctrl+O
will save the modifications you’ve made to the file
Exit Nano Command:
Ctrl+X
will close nano
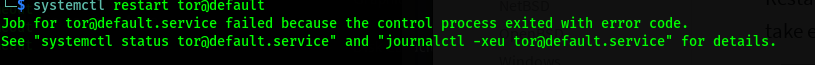
Restart tor
Add permission for yourself to read the auth cookie. With Debian Linux, the command is:
sudo usermod -a -G debian-tor [yourlinuxuser]
Logout/Login with your user to apply group changes
You can verify if your Tor setup is running correctly using:
echo ‘PROTOCOLINFO’ | nc 127.0.0.1 9051
No worries, you’re welcome - enjoy!
Tip I usually create a document with all the steps I’ve taken to set up a server, so I can refer to this document in the future & to review & reinforce my technical understanding of the actions taken.
Sometimes, actions you’ve taken in the past might not always work in the future, for example, when there’s a major OS upgrade.
Then, once I’ve learned the new way of doing something I can add it to the server document. The server document is a bit like a recipe & ensures you don’t miss any steps for future server set ups.
···
On 13/12/2021 03:43, id@parkos via Tor Project Forum wrote:
parkOS
December 13very clear thnks so much ma
Visit Topic or reply to this email to respond.
To unsubscribe from these emails, click here.
noted ill setup now 
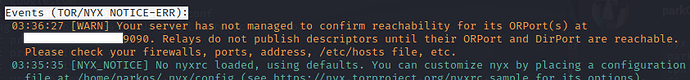
Yeah, looks like the port is firewalled. Check if you have a local firewall installed and/or if there is a firewall blocking connections at the router/switch.
You’ll see this message when the port is reachable externally:
Dec 13 14:28:44.000 [notice] Self-testing indicates your ORPort *IP*:*Port* is reachable from the outside. Excellent.
And then every 6 hours you’ll get a short heartbeat status in the log:
Dec 13 20:28:43.000 [notice] Heartbeat: Tor's uptime is 6:00 hours, with 2294 circuits open. I've sent 101.68 GB and received 99.98 GB. I've received 6351 connections on IPv4 and 1651 on IPv6. I've made 752008 connections with IPv4 and 109 with IPv6.
[...]
Dec 14 02:28:43.000 [notice] Heartbeat: Tor's uptime is 12:00 hours, with 3939 circuits open. I've sent 223.93 GB and received 219.66 GB. I've received 11021 connections on IPv4 and 2754 on IPv6. I've made 1474537 connections with IPv4 and 204 with IPv6.
latets error “Unable to find IPv6 address for ORPort 9090”
That is okay if you get the message I quoted above for IPv4. IPv6 is optional.